Hacked – Are you sure you’re secure?
Security has the been a hot topic lately. As I’m writing this article I think about all of the recent events that we hear about impacting our daily lives such as:
-
- Experts warn 2015 could be ‘Year of the Healthcare Hack – reuters.com’
- Cost of a Potential Blackout From Cybercrime: $1 Trillion – CNBC
These headlines are really quite scary. I’m certain that some, possibly many of you have experienced security issues first hand. Have you ever had to have your credit card replaced? Have you had your email compromised? How about identity theft?
These are serious and scary times we live in where breaking into our homes or businesses and taking personal and private property is something that can be done without ever physically entering a building. Why does this concern us? Because DOCSIS networks may represent a weak link the chain that a hacker is looking to exploit.
How is this possible? There are many motivations behind someone or some organization or Nation State that is targeting a person or company. It could be financial, personal, political or just for fun. In any event the attacker will look for a point of weakness. Two key points of weakness in our DOCSIS networks are the CMTS and the cable modems. As an industry we could use more dialog on securing our networks. This article is intended to bring awareness to the issue and open the dialog.
Let’s talk about the cable modem and some issues we should consider. There are some well known and Internet documented exploits on name brand cable modems. As an example, look at Vulnerability Note VU#855836 from Homeland Security on how certain modems can easily be exploited by SNMP (simple network management protocol). This hack is not limited to the vendor listed in the vulnerability note. This is more widespread as documented on a number of hacker chat rooms. Further, the researchers who investigated this hack found that they could expose the password, SSID, WPA pre-shared key, WEP keys and, in the case of one modem, the username. This basically gives a hacker complete access your home or office network if you have one of the compromised modems running the legacy firmware. Take note and be sure you are running updated firmware and are staying on top of these knowledge base issues.
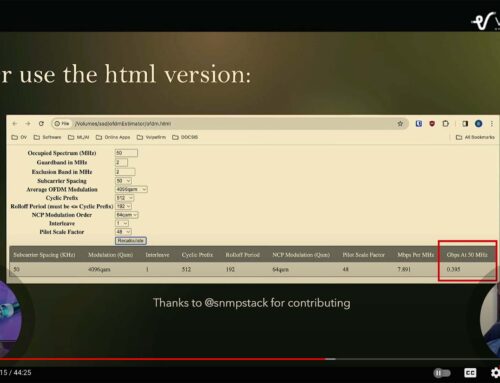
SNMP in generalis the number one way that hackers gain access into the DOCSIS network. Much of the time this is strictly for theft of service. However we can’t not always assume that is the case. In the config file that is downloaded to the cable modem there are typically two MIB strings. One that provides a read-only (RO) SNMP community string and another that provides a read-write (RW) SNMP community string. Often times administrators may find it convenient to use ‘public’ and ‘private’ as the default community strings. This is like using ‘password’ as your user password, offering little protection against hackers. It is very easy for hackers to guess these community strings and now they have access to read the data on your modem. To add one more layer of protection it is recommended to disable SNMP access at the cable modem and restrict access to IP addresses. This is done through access control lists (ACLs) on the CMTS and in the cable modem config file.
The CMTS is another point of significant opportunity for possible hackers. One of the most common issues that occurs is when a CMTS is left with a public IP address exposed for everyone to see. Sometimes this is done intentionally as the CMTS is directly connected to the network. Other times a CMTS may be temporarily connected to a public IP address for maintenance purposes. This means the CMTS becomes an opportunity for any hacker to attack it like any other computer. The most frequent occurrence are denial of service (DoS) attacks which result in the CMTS being hit with so much unwanted traffic that regular subscriber traffic is no longer able to traverse the CMTS.
So what are we to do?
There are some common steps and recommended best practices to securing your DOCSIS network.
-
- Maintain software and firmware maintenance agreements with vendors to be certain you are getting the latest bug fixes and patches for your CMTSs, cable modems and also switches & routers. You should communicate with your vendors on a regular basis to find out what security vulnerabilities they are aware of and the patches they have issued.
-
- Isolate your DOCSIS network from the public network as much as possible. What does this mean? Ideally you will never have your CMTS directly connected to a public IP address, but will have it connected to a router that is connected to a public IP address. The object is to prevent your CMTS from being directly scannable by a hacker with a router that has unified threat management capabilities (i.e. it will actively thwart hackers).
-
- Apply ACLs to your CMTS. The router will protect your CMTS from traffic off the Internet, but we still need access control lists (ACLs) to protect your internal network from hackers and malicious code inside your network. ACLs are just simple lines of code in the CMTS that instruct the CMTS what types of traffic and from what IP addresses the CMTS should trust. This means that if a subscriber connected to a cable modem tries to do something they should not, the ACL will prevent bad traffic or data from getting onto your IP network.
-
- Use the technologies built into DOCSIS to limit risks, such as Base Privacy Interface specification (BPI+), which encrypts traffic between the CMTS and cable modem and also verifies that the cable modem is valid.
-
- Use CMTS security capabilities, such as:
-
- BPI+ Policy Total – Requires modems to run BPI+
-
- TFTP Enforce – helps somewhat to limit uncapping modems
-
- DMIC – Dynamically generates config file password
-
- EAE – Early Authentication Encryption – encrypts IP & DHCP process
- Cable Privacy Hotlist (finds cloned modems)
-
- Use CMTS security capabilities, such as:
- Finally, and perhaps most importantly, have a department or person responsible for all of the above activities. For large MSOs this is the norm, but for smaller MSOs and individual cable operators, a security department may be thought of as a luxury item. However tasking a technical person with the responsibility to keep up with firmware upgrades and securing internal networks will result in significant returns when (not if) a significant network hack occurs.
As seen in BROADBAND LIBRARY
Previous events can be seen under the blog.
- If you are watching this on youtube please hit the subscribe button!
- Let us know what you think and remember to share!
- You can find slides at the bottom of the page and some on slideshare.
- Find out about events or articles by following us on Twitter, LinkedIn or Facebook too.
- We have stuff. Interested in buying some clothes with cable stuff. Click here
Also available on iTunes, Google Podcasts, Spotify, vurbl see podcasts “get your tech on”.


Leave a Reply